Every day trillions of bytes of data gets generated online & on cellular devices around the world. What most of us don’t know is that this is just scratching the surface of the enormous virtual community called the World Wide Web. The generation of data on the this online ecosystem is pretty synonymous to an iceberg on the ocean – which is only 10% above the sea level & the giant 90% of the portion lies underneath the water. Only in this case, it is even lower, that only 4% of the visible data is on top which is freely accessible and/or generated by popular websites like Google, Wikipedia & Bing etc. To take everything in perspective just look at the infographic below.
 The virtual world of the of the World Wide Web is divided into three categories:
The virtual world of the of the World Wide Web is divided into three categories:
- Surface Web (Clear Net) – consists of the indexed pages on the internet like the one you are accessing right now. Internet giants like Google & Amazon are the kings of this indexed web. Accessible to everyone – Facebook, Gmail & E-bay are examples of this type of Web.
- Deep Web (non-indexed) – It is a subset of the Internet or the major portion of the web consisting of non-indexed pages that can’t be accessed with search engines like Google or Bing. Web pages that require membership logins fall under this category – online banking, My Yahoo login or your company intranets are all examples of Deep Web although there is nothing illegal about it.
- Dark Web (Dark Net) – This is a subset of the Deep Web & the hub of mostly illegal activities. This can also be called the black market of the digital realm, but none of the content or websites can be accessed via the normal browsers like Chrome, Internet Explorer or Firefox etc.
Dark Web can be easily equated to the Digital Wild West of the Internet. This underworld Web serves as hackers’ playground, home to drugs selling & X-rated websites & even assassination portals where hit-men can be hired. Needless to say, I don’t plan to be there ever! The good thing is that accessing the Dark Web is a much more tedious task than opening up your browser & typing in the name of a website. The preferred medium of currency exchange in this black market is the Cryptocurrency kingpin, Bitcoin – one of the reasons why the authorities in the U.S have been worried sick about digital coins being used for illicit & illegal activities. Surprisingly though, Bitcoin isn’t even the most privacy- centric of the digital coins, but it is the most widely used & recognized.
The most glaring example of these Dark Net markets was Silk Road which opened in this arena in 2011 & grew to 22 million years within a year. The U.S. government was on its tail as soon as it found out about its existence, since authorities are never in favor of unregulated black markets be it in the regular economy or the digital underworld. They ended up shutting down the infamous market in 2013, but it encouraged the spawning of other such ventures most of which haven’t lasted more than 8 months to a year. Above is a timeline video of these markets to give you a snapshot.
Coming back the accessing the Dark Web – not that I am encouraging you to do it. It’s just that my curiosity of learning about everything at least, gets the better of me always. Anyways, the Dark Web can only be accessed via TOR browser bundle on the TOR network. Accessing Dark Web through a VPN (Virtual Private Network) is strongly suggested if you even intend to do so, since it keeps your security & anonymity intact – Remember there are a lot of bad actors out to get you in the Dark Web. Trying to access this part of the Web through your normal ISP spells trouble both in the real world & in the Dark Web.
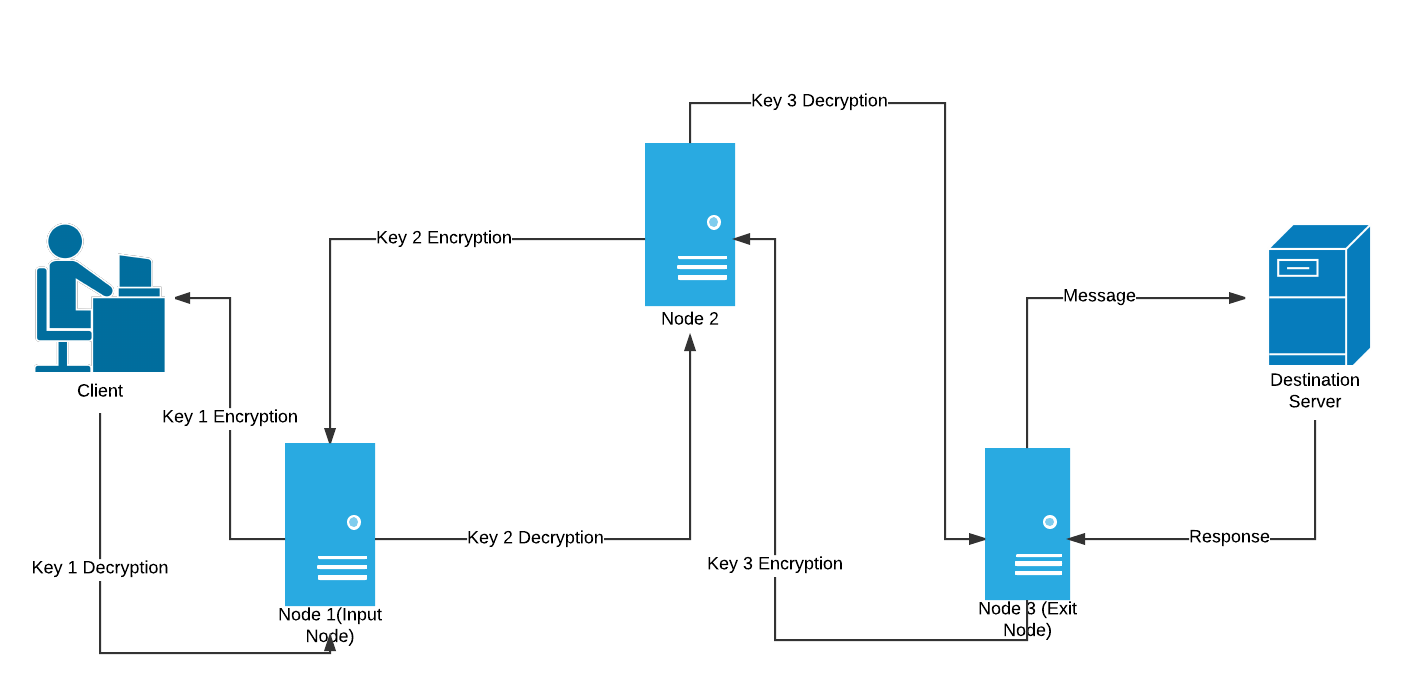
The websites here come with a .onion domain. The TOR browser uses the Onion protocol which ironically was developed by the U.S Department of Defense for secure communications. Onion protocol uses a multi-layered encryption technique as shown in the figure above, thus the analogy to the rings of an onion. It is still being used for secure communications by the military, government officials, journalists etc. in the real world but unfortunately also by the hackers, whistleblowers & other evil players on the dark side.
I guess there is & always will be a dark side to technology. We just need to know how to keep it in check so that it does not overshadow the good that has been achieved with this digital transformation.
Stay in touch: Twitter | StockTwits | LinkedIn | Telegram| Tradealike


Good article. The deep and darkwebs are not all that is out there. Back in the day, one could only access sites if you knew the IP addy, and many of those old sites remain. Usenet and IRC as well as binary-only sites were part of this loose collective, and still exist for those who look. Like you said, many are just sites of general interest or expression, not criminal enterprises. In a totally free world, one must look out for their own safety, as there are no helpful warning stickers there.
I am always curious as what darknet is… As much as I want to surf on that page there is always a hesitation on my part because i’m afraid that most of the user of darknet are hackers and I might get hack by them.
Thanks for the appreciation Alisha. As you said it was the curiosity that led me to write this article. Never knew these details until I explored it further. At least now I can say, I know better to protect myself from sinister players out there. Always on the look out for things less talked about….
I simply wanted to say thanks again. I’m not certain the things I would’ve carried out in the absence of these points provided by you regarding such field. It was before a real daunting difficulty in my view, nevertheless considering the very skilled style you treated the issue took me to jump with fulfillment. Extremely grateful for the advice and then expect you comprehend what a great job that you’re putting in training the rest all through your site. Most likely you’ve never met all of us.