With multiple solutions emerging to provide scalability to Cryptocurrencies especially Bitcoin, the debate has shifted to improving the other two segments as well - namely Privacy & Fungibility. While scalability is pretty much a universal problem for the Cryptos, Privacy focused digital coins like Monero & Zcash already exist, which employ the zk-SNARKS Zero knowledge proof to provide this capability. Bitcoin has also seen the development of
Lightning network, Rootstock Protocol &
Dandelion Privacy protocol during the past year to address the problems of high transaction costs, Scalability & Privacy.
Charlie Lee, the creator of Litecoin - one of the top 10 Cryptos by market cap & an off-shoot of the Crypto kingpin Bitcoin, implied in a tweet recently that the next frontier for digital coins would be Privacy & Fungibility. For those of you who are not familiar with the Fungibility, it relates to two different things of the same type having identical value e.g A dollar bill (cash) is basically fungible regardless of its source - coming directly from a bank or an illegal source.
"Fungibility is the only property of sound money that is missing from bitcoin and Litecoin. Now that the scaling debate is behind us, the next battleground will be fungibility and privacy. I am now focused on making Litecoin more fungible by adding Confidential Transactions."
And this is where
Mimblewimble comes into the scene with real-life implementations in
Grin &
Beam. Before you get confused any further let me clarify the terms for you. The former is the technology behind these digital coins which provides the much-needed privacy feature, while the latter two are the new cryptocurrencies on the block which are employing this privacy protocol albeit in different ways. Before breaking it down for easier understanding, here is a visual representation of the difference between a Bitcoin and a MimbleWimble transaction
.

Credit: Token Daily blog
What is MimbleWimble?
It is a privacy-focused protocol which was initially
proposed under the Pseudonym
Tom Elvis Jedusor (the French name of fictional Harry Potter character, Voldemort) in July 2016 - which was eventually
revised by
Adam Poelstra in Oct. 2016 . The protocol name itself is the name of the tongue-tying spell used in the Harry Potter series. The blockchain protocol addresses the dual purpose of bringing scalability & privacy. The original proposal was meant to improve the privacy of the Bitcoin transactions, but it hasn't received much acceptance from the Bitcoin developers, since it required changes to how the transactions are structured on the BTC blockchain currently. Recently, however, the protocol has come out of obscurity with its implementation in Grin & Beam Crypto coins. Also looking to join the bandwagon is the
Litecoin Foundation for its digital coin. The announcement stated:
"We have started exploration towards adding privacy and fungibility to Litecoin by allowing on-chain conversion of regular LTC into a MimbleWimble variant of LTC and vice versa. Upon such conversion, it will be possible to transact with MimbleWimble LTC in complete confidentiality."

How does it work?
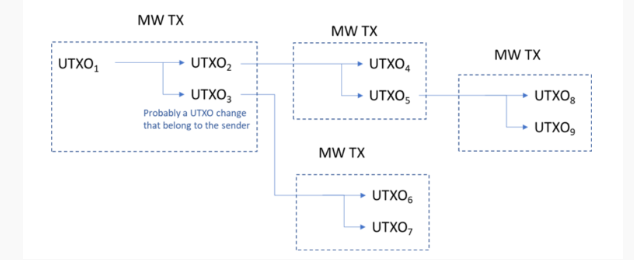
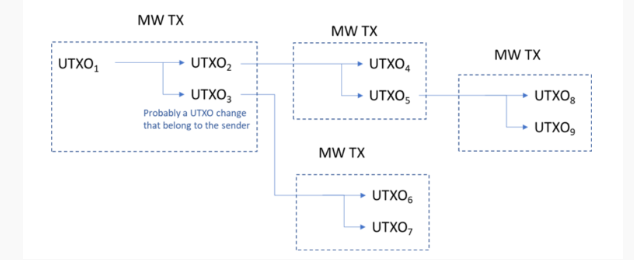
Cryptocurrencies implementing the MW protocol utilize Bitcoin’s unspent transaction
Output (UTXO) model, in which nothing is hidden. According to this model, there are three types of info that needs to be hidden to make the transaction private - sender information (TX inputs), receiver information (TX outputs) & transaction amount. MW itself achieves its purpose by employing the following two cryptographic techniques.
-
Confidential Transactions:
This system was developed by Adam Beck & later refined by Gregory Maxwell. You can hide the values of transaction amounts by utilizing Homomorphic encryption and blinding factors, where the former is an algorithm which splits the amount of value of a transaction into several parts, while the latter mixes up the transaction amounts with random numbers to further conceal the values of the split transaction amounts. Additionally in MW transaction, the receiver gets a range of blinding factors sent by the sender to act as the private key thus validating the proof of ownership and completing the transaction.
2. CoinJoins:
This cryptographic innovation was also proposed by
Gregory Maxwell. The method mixes up a pool of transactions in a way that is not possible to find out who sent money and to whom. In the MW scheme of things, a block of data would only consist of a number of inputs, outputs & signature data. The block can, however, still be verified to be valid by subtracting the total inputs from total outputs achieving a result of zero. This is a much more efficient system as compared to Bitcoin blockchain where the whole history of the block needs to be analysed to be verified and considered valid. Also this method offers significant space savings & offers execution of multiple transactions at a time.

Advantages & Shortcomings
The obvious upside to the implementation of MW is the robust privacy it offers by not only hiding the transaction amounts but by hiding the identities of the transacting parties. Public snooping is minimized by avoiding the use of visible addresses. Secondly the use of multiple transactions in a single block cuts down the block size significantly thus decreasing the processing time. Less storage requirements leave more space for extra nodes to join the network leading to better distributed & more scalable blockchain network.
On the downside, MW needs to have sender, receiver & the transaction parties to be online to validate & sign off on the transaction. This becomes a tedious exercise specially if you have multiple transactions rolled over into one block. Additionally, the unconfirmed transaction pool of the MW transactions is still visible publicly which could be used to build detailed transaction graphs of the network, thus compromising the privacy.
Comparison
Zcash shielded transactions' mechanism by encrypting the data before it even leaves your digital wallet provides superior privacy than MW. This gives an early & added layer of security. The zk-SNAKRS zero knowledge proofs still let you verify that the transaction sent was by the legitimate owner. However, the process of producing shielded address is computation-intensive, but the latest "
Sapling"upgrade on the network addressed this problem by reducing the complexity of the shielded transactions & a better adoption of the process.
Monero, on the other hand, uses Ring Confidential Transactions and stealth addresses. Ring signature is used to hide the actual signature of the sender among other irrelevant signatures. The transaction amount is hidden with the help of the confidential transaction (CT) technique - hiding of the MW transaction amount is a variant of this technique as well. Stealth addresses allow the receiver address to be only visible to transacting parties. The process was slow & expensive originally, but with "
Bulletproof" upgrade to the network, the transaction time & cost have been reduced significantly.
Grin & Beam
The launch of two new privacy-focused, Mimblewimble based Cryptocurrencies launching their Mainnets last month has been the most significant development for the promising protocol. Looking at the timeline at these two digital counterparts, Grin was the first through the gates with the technical introduction posted in Mar. 2017, with the test net launching later in November that year. Beam took off in Mar. 2018 with functional mining node and wallet client launched in the later months. There are some design & technical differences in both the projects but the most striking difference is the governance of both the projects. Grin is a community-driven, open sourced project with No ICO and focuses on decentralization. While Beam is an Israel-based startup with a team of professional developers & backed by VC funding. Simply put, both projects are working towards a similar goal but taking entirely different paths. Time will tell if either or both approaches prove successful.
MimbleWimble can still be added to the Bitcoin blockchain as a soft fork or a sidechain. All these sidechain scaling & privacy solutions for BTC & Alt. coins is a healthy development, but real-time testing like the main nets of Grin & Beam and Litecoin possibly in the near future would confirm the usability & utility of these protocols & perhaps put at ease the reluctance of the developers to adopt these scaling & privacy mechanisms.
Email?|
Twitter?
| LinkedIn?
| StockTwits?
| Telegram?