Despite a decade of increasing investments in cybersecurity, never have organizations been more vulnerable. New approaches and thinking are urgently needed.

For many companies, the cybersecurity strategy is to spend millions on security systems and services, follow best practices for patching software, and train staff … then cross fingers in the hopes that the next breach won’t be as bad as the last.
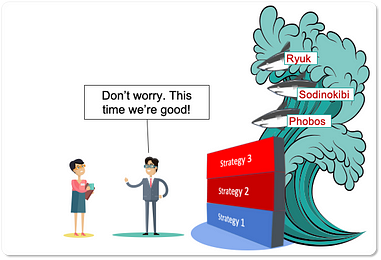
Apparently, the above strategy isn’t a good one for companies when judging by the data. Breaches are becoming more and more commonplace, expensive, and disruptive. [1] Congress’s Solarium Security Report states that as a nation, “we are dangerously insecure in cyber.” [2] A recent study found that cybersecurity solutions only prevented 33% of attacks and generated an alert only 9% of the time. [3]
Such is the daily news cycle of breaches and ransom payments that you’re forgiven if you take the term “cybersecurity” as a wry joke and a fully qualified oxymoron.
Companies are sandwiched between the security vendors and the cybercriminals, paying out to both sides. Organizations purchase security products from the security vendors and insurance policies from insurers. When inevitably breached, organizations pay ransom to cybercriminals, incur higher premiums from insurers, and pay regulatory fines all while losing business. The more that companies are compromised, the more security products and insurance they need, which drives increased sophistication of the cybercriminals, and the cycle repeats. It’s a pretty good business unless you’re the company in the middle.
So profitable has the cybersecurity-criminal cycle become that worldwide spending on cybersecurity is forecasted to reach $133.7 billion in 2022. [4] While on the other side of the coin, cybercrime is now so wonderfully lucrative that ransomware-as-a-service is a thing and cybercriminal groups are forming syndicates, all signs of a thriving ecosystem. [5] In Q1 of 2020 the average cost of a ransomware payment was up 33% to $111,605. [6]
When a market is so lucrative, you can be sure that things won’t change much — at least not by the benefiting parties.

So, as we wait for a silver bullet with our checkbooks out, hoping for the latest vendor’s promised AI and quantum powered security tool, we should remember that cybercriminals will also use AI and quantum powered hacking tools. [7]
Doing the same thing and expecting different results, clearly isn’t working as a corporate cybersecurity strategy.
If you’re not a security vendor or a cybercriminal, it is time to completely reimagine how we secure the digital organization. All trends for costs borne by the company are going up and have been for a long time. More recently, things have gotten worse. According to IBM, “… organizations in the 2019 study were nearly one-third more likely to experience a breach within two years than they were in 2014.” [1] At what point do we accept that we’re going in the wrong direction with regards to securing the company? Doing the same thing and expecting different results, clearly isn’t working as a corporate cybersecurity strategy.
The safest defense is to simply unplug from the Internet. But we can’t. That in itself would destroy an organization. We are entangled in a gordian knot. We need to stay connected, but how we’re connected is too dangerous. The way we use technology is such that it is impossible to keep threats out while simultaneously keeping technology usable and empowering for the workforce. What we need to do is rethink the entire topology of our technology. We need a knife to cut the knot.
We need a knife to cut the knot.
Rethinking the entire topology of technology is a huge statement and an even larger undertaking. Like anything really big, identifying the low hanging fruit can be … a fruitful place to start. Once understood, a glaring and frankly surprising opportunity is a technology literally under our collective noses — on our cell phones, laptops, everywhere. It is the most ubiquitous file-sharing technology on the planet and has been since the inception of the Internet. Today it is a primary cause of data sprawl and loss. [8] It spreads corporate data with unprotected, untraceable abandon, and is a vector of choice for cybercriminals wanting to infect their targets with malicious code. [9] It is so pervasive that, like the air we breathe, it is virtually invisible. This invisible menace is email and specifically email attachments.
It is a costly irony that while organizations pour their treasures into defending their data, they continue to embrace an insecure 50-year-old file-sharing technology that leaks their data with viral efficiency. [10]

The email attachment is a technology long overdue for the dustbin of history. Its replacement has arrived in the form of a secure, purpose-built, file-sharing technology called cloud storage (e.g., Box, Egnyte, Google Drive, MS OneDrive). Cloud storage allows for the sharing of files through secure connections, pointing back to a single defensible repository. It avoids the inherent data sprawl intrinsic to email and thus reduces file duplication by a factor of 10x. [11] Files shared through cloud storage links can be controlled, require authentication, automatically be expired, and monitored when shared externally. With cloud storage links, a network breach is very different. With standard email, criminals have easy, unrestricted access to all attachments. Not so if instead of email attachments, emails share files as secure cloud storage links. The cybercriminal has many more steps to steal data, needing to follow each link and get past multiple access controls from user credentials to unusual activity monitoring (Box Shield). Forcing attackers to take extra steps is a powerful and proven deterrent to cybercrime. [12]
The cybersecurity knot is large, but we can cut one particularly sizable strand by replacing our long term dependence on email attachments as a means of file sharing. Of course, getting users to abandon their age-old habits is not easy, but it is becoming easier as major email vendors like Microsoft and Google build in shortcuts to use cloud storage links in place of attachments. Furthermore, technologies, like mxHero Mail2Cloud, help automate the replacement of email attachments with best-of-breed cloud storage service links.
There are more strands to cut in the gordian knot of cybersecurity. Replacing email attachments with cloud storage links can serve as a concrete example of how organizations can reshape their digital topology so that it becomes fundamentally more robust. In this way, we envision a different security strategy. Instead of only focusing on perpetual and futile wall building against external threats, we also address the fundamental structural vulnerabilities of the organization. Through fundamental change, we aim to entirely alter the rules of the game which today we can not win. Instead of adding to our failing walls, maybe we should simply move inland, safely away from the sea.

Sources
- Cost of a Data Breach Report 2019, IBM
- America Under Fire — US Gov. Solarium Cybersecurity Report Sounds The General Alarm
- Mandiant Security Effectiveness Report
- Gartner Forecasts Worldwide Information Security Spending to Exceed $124 Billion in 2019
- Ransomware as a service (RaaS): What is it and How Does It Work?
- Ransomware Payments Up 33% As Maze and Sodinokibi Proliferate in Q1 2020, Coveware
- Mitigating Business Risk and Driving Business Value with Behavior-Based AI Security, IDC
- Our Dangerous Reliance on Email Attachments And What To Do About It
- 2020 Data Breach Investigations Report, Verizon
- The Futility (And Hope) Of Cybersecurity In Today’s Organizations | Data Driven Investor
- Containing Data Sprawl In The Work-At-Home Era of COVID-19 And Beyond
- A Critical Defensive Layer Missing From Most Security Strategies

